
When searching for the Kiro management console in CloudTrail, I caught a glimpse of the integrated infrastructure
This page has been translated by machine translation. View original
When translating AWS's generative AI coding assistant "Kiro", an Enterprise feature for user activity reporting was added in February 2026. To utilize this report, I investigated how to retrieve subscription information displayed in Kiro's management console via API. By identifying endpoint information from the console's HTML source and observing actual API calls with CloudTrail, I sent requests with SigV4 signatures to the discovered private API, revealing the existence of a subscription foundation that integrates management of both Kiro and Q Developer.
The verification in this article was conducted on an AWS account opened temporarily for research purposes. I used AdministratorAccess permissions, and this is not an environment intended for permanent operation.
Looking for clues in the dashboard HTML source
First, let's examine the dashboard's HTML source. This is public information that can be checked with the browser's developer tools.
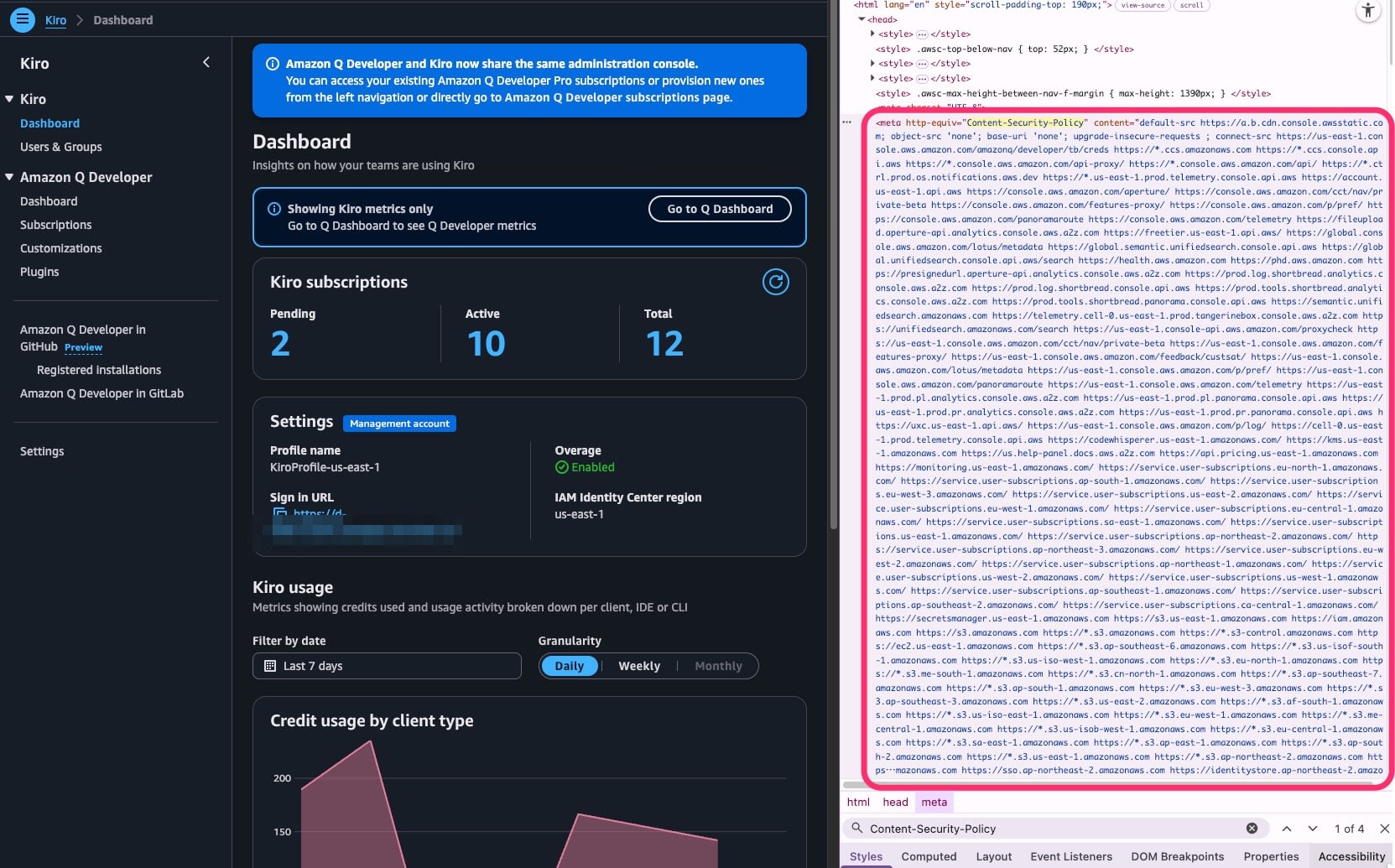
CSP connect-src endpoint analysis
The Content Security Policy (CSP) connect-src directive lists endpoints that the dashboard is allowed to communicate with. Extracting only endpoints containing amazonaws.com in the browser's DevTools Console revealed 134 items.
(Capture: List of amazonaws.com endpoints extracted from CSP connect-src)
Among these, the endpoints related to Kiro management are as follows:
| Category | Endpoint | Purpose |
|---|---|---|
| codewhisperer | codewhisperer.us-east-1.amazonaws.com | Profile management |
| user-subscriptions | service.user-subscriptions.{region}.amazonaws.com (17 regions) | Subscription management |
| sso / identitystore | sso.{region}.amazonaws.com (17 regions) | Identity Center integration |
| kms | kms.us-east-1.amazonaws.com | Encryption key management |
| secretsmanager | secretsmanager.us-east-1.amazonaws.com | Secret management |
| pricing | api.pricing.us-east-1.amazonaws.com | Pricing information |
| monitoring | monitoring.us-east-1.amazonaws.com | CloudWatch integration |
| codeconnections | codeconnections.us-east-1.amazonaws.com | Repository integration |
Notable is user-subscriptions. It exists in 17 regions and appears to be the core of subscription management. However, this service name does not appear in AWS's official documentation.
Discovery of internal codenames
More interesting information was embedded in the HTML meta[name="tb-data"] tag.
The string zorn appears with keys like zornEndpoints and zornServicePrincipal. This is likely the internal codename for the user-subscriptions service, but its identity is unknown at this point. Another string, tangerinebox, was also found. This is the telemetry foundation for the AWS console.
Feature flags (33)
33 feature flags were found in meta[id="meta-features-json"]. All are enabled: true.
| Category | Flag count | Examples |
|---|---|---|
| Kiro specific | 2 | kiro-pricing, kiro-console |
| MCP | 2 | mcp-configuration, mcp-registry-url |
| Q Developer derived | 11 | q-extensions, q-agent-for-*, etc. |
| Dashboard/Infrastructure | 18 | merge-old-dashboard, cloudzero-plugin, etc. |
There are only 2 Kiro-specific flags. The remaining 31 are for Q Developer and the dashboard infrastructure. This suggests that Kiro largely shares Q Developer's management foundation.
Observing private APIs with CloudTrail
Now that we know the communication target services from CSP analysis, let's check which APIs are actually being called using CloudTrail.
Filtering method
Opening the AWS console triggers many API calls for EC2, ResourceGroup, etc., creating lots of noise. Since we know the service names from CSP analysis, we filtered by EventSource.
aws cloudtrail lookup-events \
--start-time "2026-02-18T18:28:00Z" \
--end-time "2026-02-18T18:37:00Z" \
--region us-east-1 \
--output json \
| jq '[.Events[] | select(.EventSource == "codewhisperer.amazonaws.com" or
.EventSource == "user-subscriptions.amazonaws.com" or
.EventSource == "q.amazonaws.com")]'
Observation results: 3 services, 14 APIs
I observed 39 events during dashboard access (18:28-18:37 UTC). Of these, 14 APIs across 3 services were Kiro-related.
codewhisperer.amazonaws.com (3 APIs)
| API | Purpose |
|---|---|
ListProfiles |
Profile list |
GetUsageLimits |
Usage limits (origin: AI_EDITOR or KIRO_CLI) |
ListTagsForResource |
Resource tags |
user-subscriptions.amazonaws.com (3 APIs)
| API | Purpose |
|---|---|
ListUserSubscriptions |
★ List of subscriptions for all users |
ListApplicationClaims |
Application claims |
ListClaims |
Claims (identityProvider: BUILDER_ID) |
q.amazonaws.com (8 APIs)
| API | Purpose |
|---|---|
ListDashboardMetrics |
★ Dashboard metrics (dashboardType: KIRO, granularity: DAILY) |
CreateAssignment / UpdateAssignment |
Subscription management |
SendMessage, ListConversations |
Chat |
GetIdentityMetadata |
ID information |
ListPluginProviders, ListPlugins |
Plugin management |
Calling APIs with SigV4 signatures
Why can't we call them normally?
Normally, you can call AWS services with aws <service> <operation>. However, user-subscriptions and q are private services with no service definitions in the AWS CLI, so neither CLI nor SDK can be used.
Therefore, we need to manually apply SigV4 (Signature Version 4), AWS's HTTP request authentication mechanism.
Normal: aws cli → SigV4 signing in SDK → HTTP request → AWS service
This time: Python → Signing with botocore.auth.SigV4Auth → HTTP request → Private service
Implementation
We call it as a path-based Coral API (POST /{OperationName} + JSON body).
from botocore.auth import SigV4Auth
from botocore.awsrequest import AWSRequest
import requests, json, boto3
session = boto3.Session(region_name='us-east-1')
creds = session.get_credentials().get_frozen_credentials()
url = "https://service.user-subscriptions.us-east-1.amazonaws.com/ListUserSubscriptions"
payload = json.dumps({
"instanceArn": "arn:aws:sso:::instance/ssoins-XXXXXXXXXXXXXXXX",
"maxResults": 1000,
"subscriptionRegion": "us-east-1"
})
req = AWSRequest(method='POST', url=url, data=payload,
headers={'Content-Type': 'application/json'})
SigV4Auth(creds, 'user-subscriptions', 'us-east-1').add_auth(req)
resp = requests.post(req.url, headers=dict(req.headers), data=req.body)
print(json.dumps(resp.json(), indent=2))
Of the 14 APIs, only ListUserSubscriptions in user-subscriptions was successfully called. CodeWhisperer APIs returned 429 or UnknownOperation, and q APIs returned 500 or UnknownOperation, showing that different API protocols are mixed across the 3 services.
ListUserSubscriptions execution results
Cross-user retrieval
All users of both Kiro and Q Dev Pro were returned in a single response.
KIRO_ENTERPRISE_PRO: 12 users
ACTIVE: 10 people
PENDING: 2 people (not yet logged in)
This information exactly matches the "User subscriptions" screen in the dashboard. Subscription types other than Kiro (e.g., Q_DEVELOPER_STANDALONE) were also included in the same response. Since Kiro and Q Developer subscriptions were registered to this account's Identity Center, information for users of both services was returned together.
Kiro user list (masked)
| User | Subscription | activated | aggregated |
|---|---|---|---|
| user-A | KIRO_ENTERPRISE_PRO | 2025-12-12 | GROUP |
| user-B | KIRO_ENTERPRISE_PRO | 2025-12-04 | GROUP |
| user-C | KIRO_ENTERPRISE_PRO | 2025-12-08 | GROUP |
| user-D | KIRO_ENTERPRISE_PRO | 2025-12-12 | GROUP |
| user-E | KIRO_ENTERPRISE_PRO | 2025-12-05 | GROUP |
| user-F | KIRO_ENTERPRISE_PRO | 2025-12-11 | GROUP |
| user-G | KIRO_ENTERPRISE_PRO | 2026-02-09 | GROUP |
| user-H | KIRO_ENTERPRISE_PRO | 2026-01-01 | INDIVIDUAL_AND_GROUP |
| user-I | KIRO_ENTERPRISE_PRO | 2026-02-12 | GROUP |
| user-J | KIRO_ENTERPRISE_PRO | 2025-12-08 | GROUP |
The identity of zorn — Subscription integration platform
The mystery of the internal codename zorn (zornEndpoints, zornServicePrincipal) discovered in the HTML source is now revealed.
zorn = user-subscriptions service. It's the backend platform that integrates subscription management for both Kiro and Q Dev Pro. A single API call returns all subscriptions across service boundaries.
| Internal name in API | Meaning | Status |
|---|---|---|
KIRO_ENTERPRISE_PRO |
Kiro PRO ($20/month) | ACTIVE / PENDING |
Q_DEVELOPER_STANDALONE |
Q Developer Pro | ACTIVE |
Q_DEVELOPER_BENEFIT |
Q Dev Pro accompanying subscription | ACTIVE (GROUP) |
Q_BUSINESS |
Q Business integration slot | Almost all PENDING |
While CreateAssignment / UpdateAssignment in CloudTrail used names like Q_DEVELOPER_STANDALONE_PRO / Q_DEVELOPER_STANDALONE_PRO_PLUS, ListUserSubscriptions used the unique name KIRO_ENTERPRISE_PRO. The internal names differ by API operation even for the same subscription.
Differences between Kiro and Q Developer subscriptions
Comparing the responses revealed several differences in the subscription systems of Kiro and Q Dev Pro.
Q Developer Pro automatically grants an accompanying subscription called Q_DEVELOPER_BENEFIT, but this is not granted to Kiro users. Kiro and Q Dev Pro are separate subscription systems.
The aggregatedSubscriptionType indicating the assignment method is GROUP for SSO group assignments, and INDIVIDUAL_AND_GROUP if both individual and group assignments exist. The latter applies to users who personally upgraded from PRO to PRO+ as mentioned in the month-end upgrade article.
Also, while some subscription types recorded lastActivityDate, all Kiro users (KIRO_ENTERPRISE_PRO) had null. It seems Kiro usage is not tracked through this API.
Q_BUSINESS PENDING for all users
Even users with only Kiro contracts had Q_BUSINESS: PENDING assigned. This is residual data from when Amazon Q Business SSO configuration was tested. PENDING indicates that a license slot has been allocated but the user has never accessed the service.
Why two services coexist
The coexistence of Kiro and Q Dev Pro within the same Identity Center, retrievable by a single API, is likely due to the phased migration from CodeWhisperer → Q Developer → Kiro. The backend management platform (zorn) integrates management of multiple subscription types, while only the dashboard GUI is separated by service.
Summary
Overall architecture
Behind the dashboard is a configuration where three services—zorn (user-subscriptions), codewhisperer, and q—work together.
While this verification comes with no guarantees, ListUserSubscriptions allowed us to directly confirm the data behind the console, resulting in interesting findings that satisfied technical curiosity.
The backend revealed a glimpse of how Kiro and Q Developer Pro are managed on an integrated data platform (zorn), so when official management APIs are provided in the future, I'd like to compare them with the data structures observed in this article.