![[Report] SEC302-R : AWS Network Firewall and DNS Firewall security in multi-VPC architectures#reinvent](https://devio2023-media.developers.io/wp-content/uploads/2022/11/eyecatch_reinvent2022_session-report.png)
[Report] SEC302-R : AWS Network Firewall and DNS Firewall security in multi-VPC architectures#reinvent
この記事は公開されてから1年以上経過しています。情報が古い可能性がありますので、ご注意ください。
Session Overview
This is a workshop session about "AWS Network Firewall and DNS Firewall security in multi-VPC architectures".
This workshop guides participants through configuring AWS Network Firewall and Amazon Route 53 Resolver DNS Firewall in an AWS multi-VPC environment. It demonstrates how VPCs can be interconnected with a centralized AWS Network Firewall and DNS Firewall configuration to ease the governance requirements of network security.
Speakers
Session Level
300-Advanced
Session type
Workshop
Report
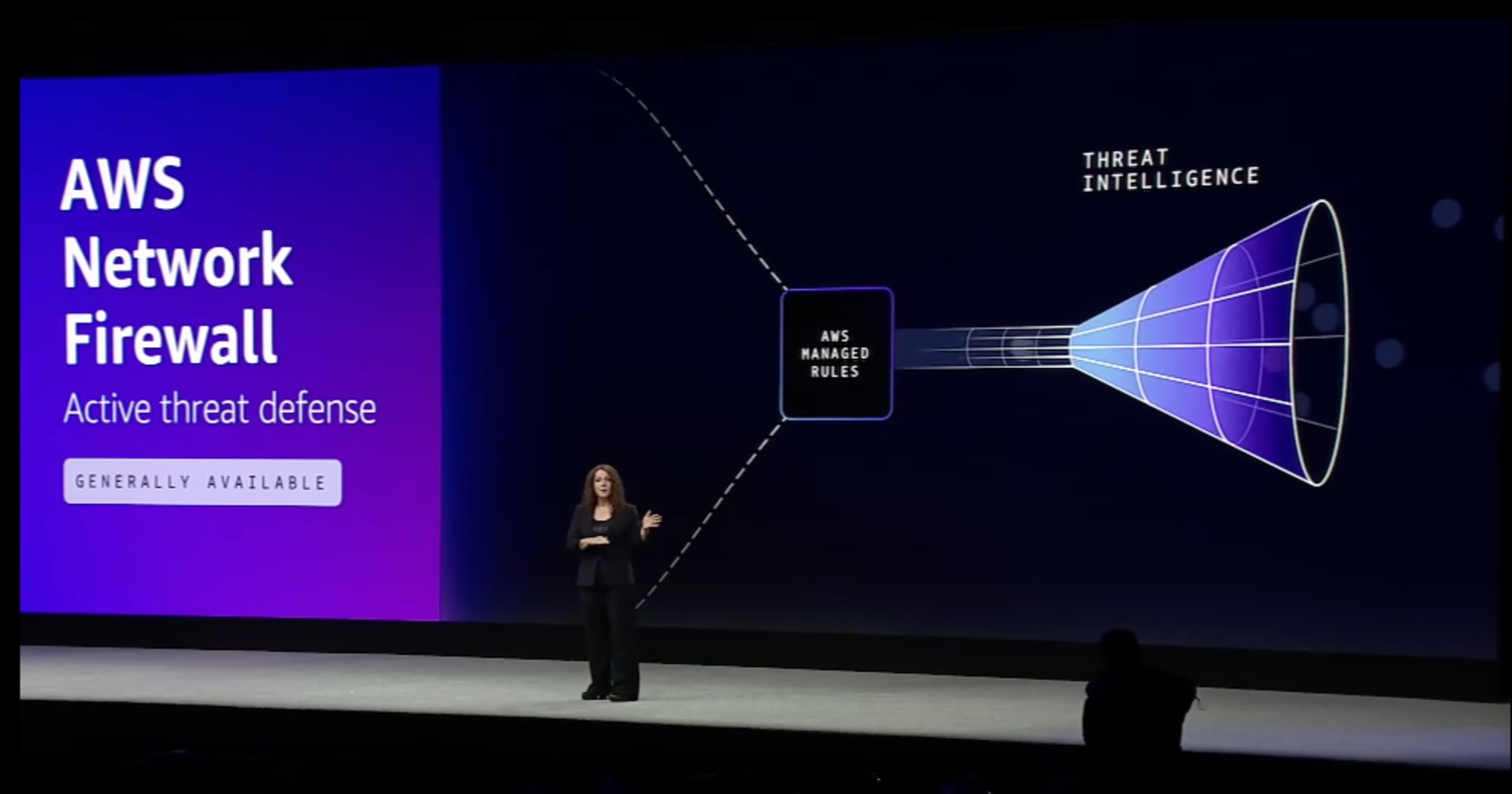
AWS Network Firewall
AWS Network Firewall is a managed service that provides protection controls for virtual networks. AWS Network Firewall is a firewall service for the VPC. With Network Firewall you can easily inspect, detect and filter web traffic. The Network Firewall resides in AWS Managed VPC and scales automatically with traffic.

Since the Network Firewall scales automatically, it is not required to deploy and manage any infrastructure. All the requests passing through VPC can be routed through AWS Network Firewall. And also the requests from resources in a VPC can also route through AWS Network Firewall. The Network Firewall logs can be published to Amazon S3, Amazon Kinesis, Amazon Cloudwatch and other Partner Solutions.

There are 3 main features of a Network Firewall:
- Packet filtering
- Visibility and reporting
- Central management
Refer to the below image for more information about each feature of the Network Firewall.

The below image describes the difference between Network Firewall and other AWS security services.

Deployment models
Distributed deployment model
In the distributed deployment model, AWS Network Firewall is deployed into each VPC. It is not required to connect VPCs and each AWS Network Firewall has its own firewall policy or shares a policy through common rule groups.

Centralized deployment model
Transit Gateway is required in a centralized deployment model for connecting VPCs. The Network Firewall deployed in a centralized model performs Inter-VPC inspection and Internet traffic filtering.

Combined deployment model
The combined deployment model is basically a combination of both Distributed and Centralized deployment models. The Network Firewall performs Inter-VPC inspection and Internet traffic filtering in this case as well.

Amazon Route 53 Resolver DNS Firewall
Amazon Route 53 Resolver DNS Firewall is a Firewall for Route 53 Resolver. It is a managed service that inspects DNS traffic. With this, the traffic can be easily denied/allowed across all VPCs centrally. Route 53 Resolver DNS Firewall is highly available.

Features of DNS Firewall
- DNS Filtering - filters traffic based on Domain name.
- Central management - manages cross-account using AWS Firewall Manager.
- Managed rules - Domain name-based managed rules for filtering traffic.
- Visibility and reporting - The Firewall can be configured to send logs to S3, Cloudwatch or Kinesis.

Architecture Diagram
The below image shows a combined architecture diagram of the AWS Network Firewall and DNS Firewall.

Summary
This was a workshop session, so there was a hands-on lab about AWS Network Firewall configuration using either Distributed Deployment Model or Centralized Deployment Model.
Refer to the following document to know more about AWS Network Firewall and it also contains the workshop lab.