AWS WAF v2のS3へのログ出力をAWS CDK(一部AWS CLI)で設定してみた
この記事は公開されてから1年以上経過しています。情報が古い可能性がありますので、ご注意ください。
こんにちは、CX事業本部の若槻です。
前回のエントリでは、AWS WAFv2のWebACLの作成とCloudFrontへの適用をAWS CDKで行いました。
このAWS WAFv2にはログ出力の設定がありますが、そのためには別途FirehoseでDeliveryStreamを作成して紐付ける必要があります。
今回は、AWS WAF v2のFirehoseを使用したS3へのログ出力をAWS CDK(一部AWS CLI)で設定してみました。
やってみた
前回エントリで作成したリソースに修正を加える形で手順をご紹介します。
CDKモジュール追加
% npm i @aws-cdk/aws-kinesisfirehose @aws-cdk/aws-logs
CDKスタックへのリソース追加
ハイライト箇所が追記部分です。
[ts title="waf-firehose-stack.ts" highlight="7,8,169-251"]@
このCDKスタック中ではWebACLとDeliveryStreamの紐付けは行いません。@aws-cdk/aws-wafv2のドキュメントを見る限り、紐付けるためのプロパティがなく出来ないためです。
よって紐付けの設定のみAWS CLIで手動で行います。
CDKデプロイ
% cdk deploy
WebACLとDeliveryStreamを紐付ける
まずWebACLとDeliveryStreamのArnを確認します。(CDKスタック内でconsole.logでも確認可能です)
REGION=us-east-1
ACCOUNT_ID=XXXXXXXXXXXX
% aws wafv2 list-web-acls \
--scope CLOUDFRONT \
--region ${REGION}
% aws firehose describe-delivery-stream \
--delivery-stream-name aws-waf-logs-demo \
--region ${REGION} \
--query DeliveryStreamDescription.DeliveryStreamARN
下記のコマンドで両者のArnを指定して紐付けます。
% aws wafv2 put-logging-configuration \
--logging-configuration \
ResourceArn=${WEB_ACL_ARN},LogDestinationConfigs=${FIREHOSE_DELIVERY_STREAM_ARN} \
--region ${REGION}
動作確認
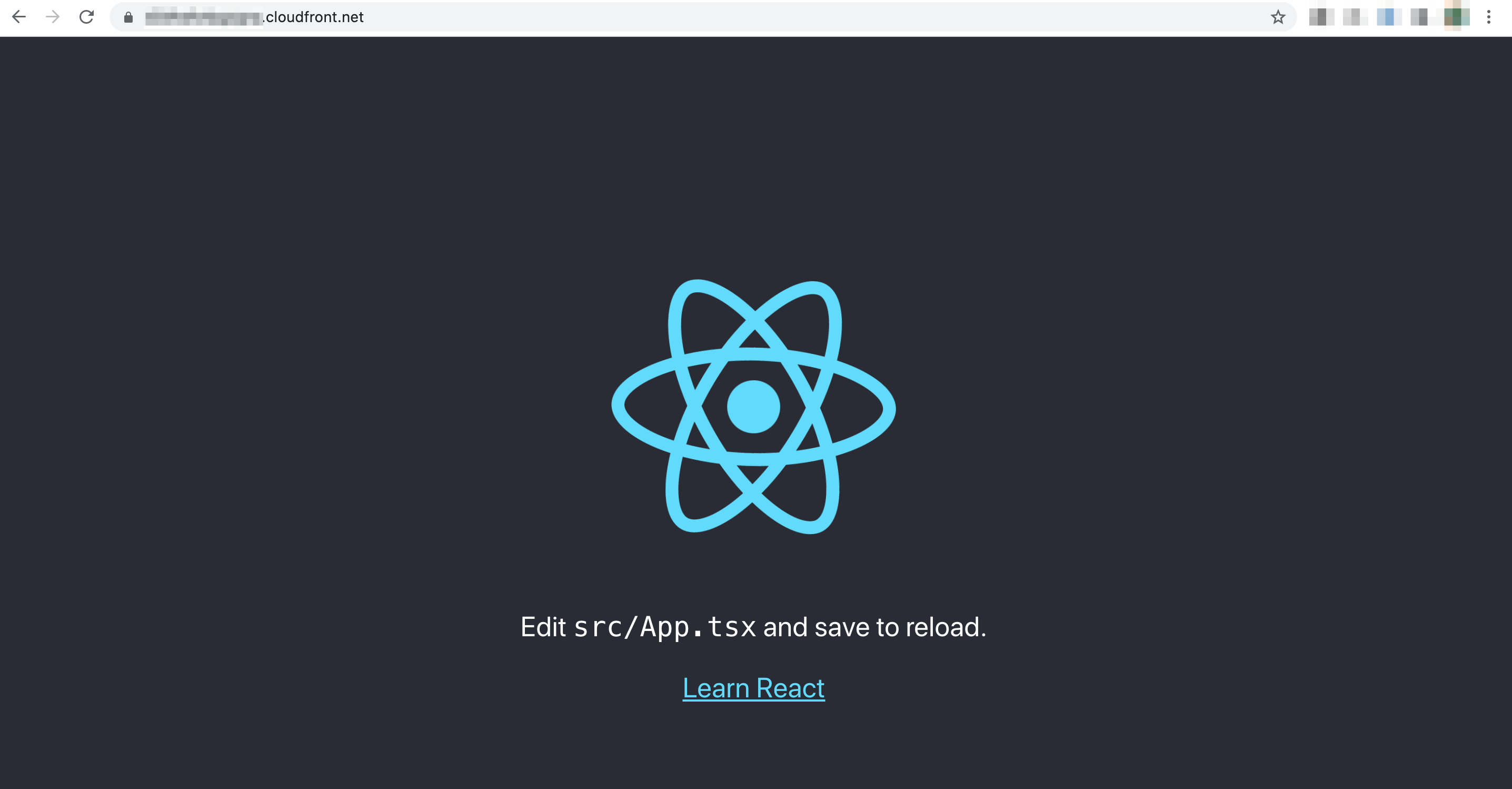
WebACLが適用されているCloudFrontがホストしているWebサイトにアクセスします。
10分ほどしたらS3バケットのlogsプレフィクス配下にログが作成されました。
% aws s3 ls s3://aws-waf-logs-demo-${REGION}-${ACCOUNT_ID} --recursive
2021-06-10 19:04:27 1559 logs/2021/06/10/09/aws-waf-logs-demo-1-2021-06-10-09-58-08-9864cb19-1d2e-4a57-9e30-0ddfdca6f5e3.gz
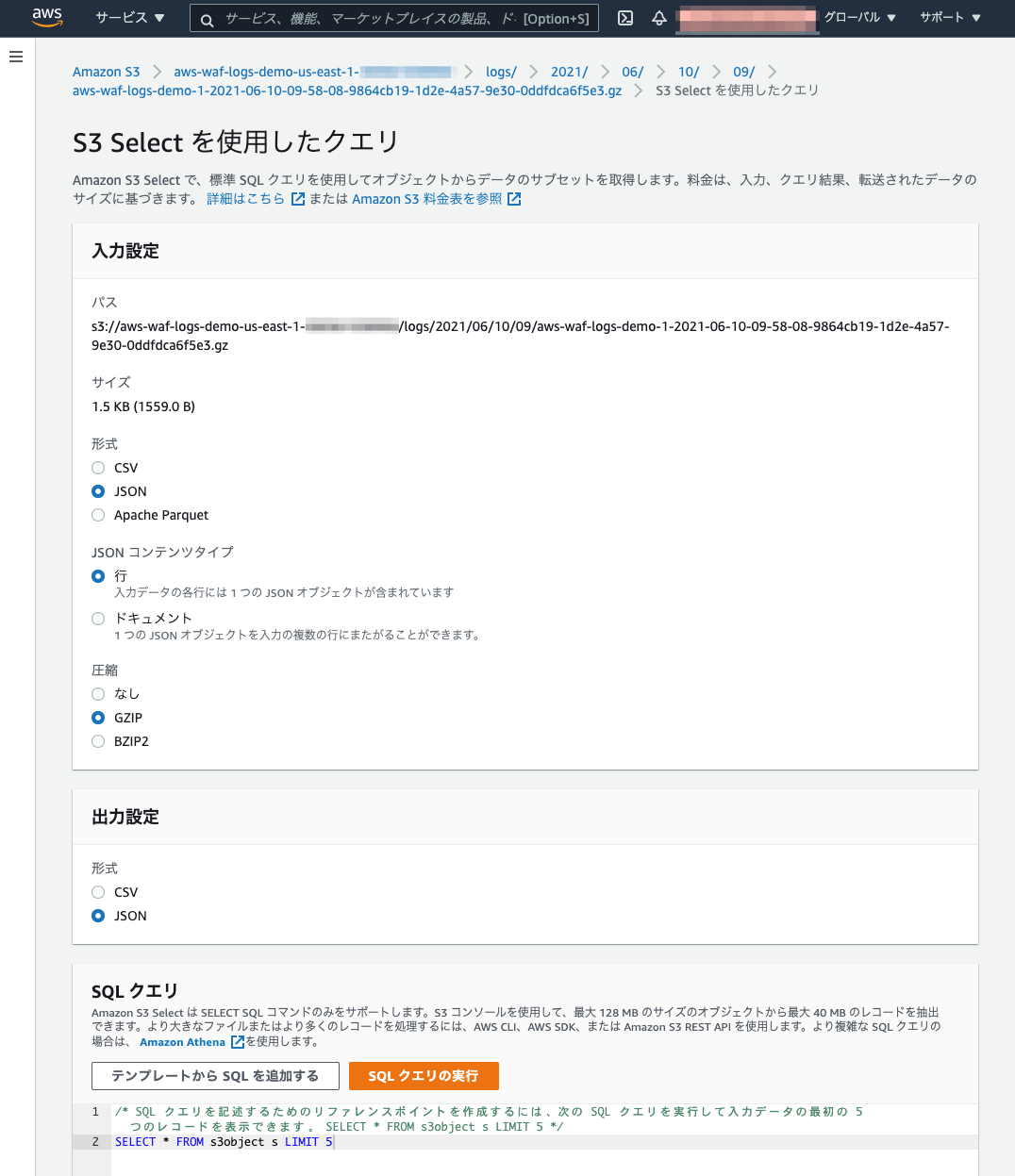
S3 SELECTを使用して下記のような指定でログの内容を確認できました。
- 入力設定
- 形式:JSON
- JSONコンテンツタイプ:行
- 圧縮:GZIP
- 出力設定
- 形式JSON
WebACLのログのフィールド仕様は下記ドキュメントから確認可能です。
Log Examples
{
"timestamp": 1576280412771,
"formatVersion": 1,
"webaclId": "arn:aws:wafv2:ap-southeast-2:EXAMPLE12345:regional/webacl/STMTest/1EXAMPLE-2ARN-3ARN-4ARN-123456EXAMPLE",
"terminatingRuleId": "STMTest_SQLi_XSS",
"terminatingRuleType": "REGULAR",
"action": "BLOCK",
"terminatingRuleMatchDetails": [
{
"conditionType": "SQL_INJECTION",
"location": "HEADER",
"matchedData": [
"10",
"AND",
"1"
]
}
],
"httpSourceName": "-",
"httpSourceId": "-",
"ruleGroupList": [],
"rateBasedRuleList": [],
"nonTerminatingMatchingRules": [],
"httpRequest": {
"clientIp": "1.1.1.1",
"country": "AU",
"headers": [
{
"name": "Host",
"value": "localhost:1989"
},
{
"name": "User-Agent",
"value": "curl/7.61.1"
},
{
"name": "Accept",
"value": "*/*"
},
{
"name": "x-stm-test",
"value": "10 AND 1=1"
}
],
"uri": "/foo",
"args": "",
"httpVersion": "HTTP/1.1",
"httpMethod": "GET",
"requestId": "rid"
},
"labels": [
{
"name": "value"
}
]
}
おわりに
AWS WAF v2のFirehoseを使用したS3へのログ出力をAWS CDK(一部AWS CLI)で設定してみました。
WebACLのログからアクセスのAllow/Block/Countの状況を確認して、ルールの最適化を行いたい場合にこの設定がされていると便利ですね。
参考
- Amazon S3 にログを保存するように AWS WAF の包括的なログ記録を設定する
- AWS CDKでAPI GatewayからKinesis Data Streamsにデータを流す設定を作成してみた | DevelopersIO
- AWS WAFのLogを保存するKinesis FirehoseをCloudFormationでさくっと作ってみた | DevelopersIO
以上